Enhancing Security and Simplifying Identity Management for a Leading Global Appliances Player
A popular worldwide brand that offers a comprehensive range of solutions for spaces, including homes, offices, stores, and other commercial facilities specializes in creating appliances for multiple purposes, such as life solutions like electrical construction and housing materials, IoT-connected solutions for B2B, innovative devices and appliances for the auto industry, and a diverse range of products and services for the industrial sector.

Manufacturing Industry
Published Date : 19-May-2023
Better control over AWS accounts and Access management
The client had a crucial need to streamline their AWS accounts due to multiple isolated environments and distributed authentication mechanisms. These environments were in the form of different AWS accounts, which resulted in no centralized user access visibility and control. The organization wanted to implement standardized AWS best practices for identity & access management to maintain their organization’s security standards.
Their requirements primarily included :
- Centralized access controls for AWS environment access.
- Prevention of unauthorized access on AWS landing zone accounts
- Centralized access on AWS accounts & Resources with Single Sign-on.
- Centralized dashboard for continuous visibility into an AWS environment.
- Consolidated billing
- Dedicated AWS accounts for a specific type of workload including security, Development, logging, UAT, Production etc.
- Protection of Multi-cloud infrastructure from various attack vectors.
- Malware protection for environment
Centralized Access Control & Visibility for the Client
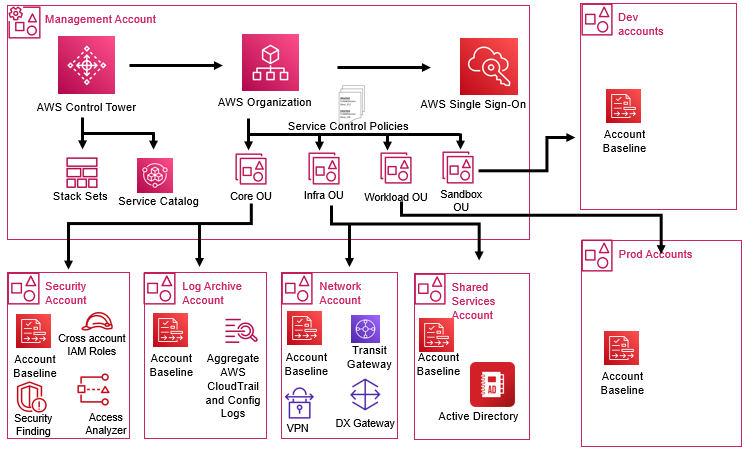
Umbrella Infocare proposed a solution for the global appliances giant to utilize the AWS landing zone with AWS Control Tower & AWS IAM identity center. This allows the customer to monitor and control their identity & access mechanism for their AWS environment centrally in line with the organization’s security standards. Landing zone also provides automation of organization structure setup using best practices and the creation of new accounts with pre-approved configurations.
Solution Overview :
- Access management for various AWS environments with MFA control using AWS IAM Identity Center.
- SSO authentication for AWS account and resources.
- Centralized access mechanism for AWS instances & applications using On-premises Active Directory and additional domain control (ADC).
- Role-based access for cross-application authentication. Access to AWS services with least privilege custom permission sets.
- Role-based access to AWS services for 3rd party partners and contractors.
- Detection of MFA for IAM & root users' console access using guard rails.
- Prevention of configuration changes for underlying implementation using service control policies (for preventive guardrails)
- Continuously detect configuration changes through AWS Config rules (for detective guardrails)
- Update the guardrail status on the Control Tower dashboard.
- Disallow access to unauthorized read\write access to log archive, S3 buckets. Mandating the encryption on EBS volumes.
- Monitoring of user access.
- Establish a configuration baseline using AWS CloudFormation
- Malware detection and Prevention solution.
AWS Services used
- AWS Control Tower
- AWS Identity Centre
- AWS Config
- AWS WAF
- AWS Organization
- AWS Security Hub
- AWS Guard Duty
- AWS Cloud Trail
- AWS Inspector
- VPC Flow logs
- AWS Key Management service
Architecture
Enhanced Security & better Identity management
Umbrella Infocare’s proposed solution provided several benefits to the client. It streamlined and standardized their AWS accounts, enhanced security, and ensured compliance with organizational standards. The solution provides centralized identity management and disallowed unauthorized access to sensitive data. The solution also gives preventive and detective guardrails to continuously detect and stop configuration changes.
A host-based security solution is deployed to prevent malware, such as viruses, worms, and ransomware. XDR complements this by enhanced monitoring and bolstering overall security measures.
Key benefits include :
- Centralized Identity & Access Management for AWS access
- Secure access using Multi-Factor Authentication
- Centralized access for instances and applications using ADC
- Standardization of provisioning new accounts.
- Disallow usage of disabled AWS region
- Centralized Management of encryption keys
- Billing management
- Standardized account level control using guard rails.
- Dedicated account for logs.
- Centralized network connectivity
- Malware protection for the host